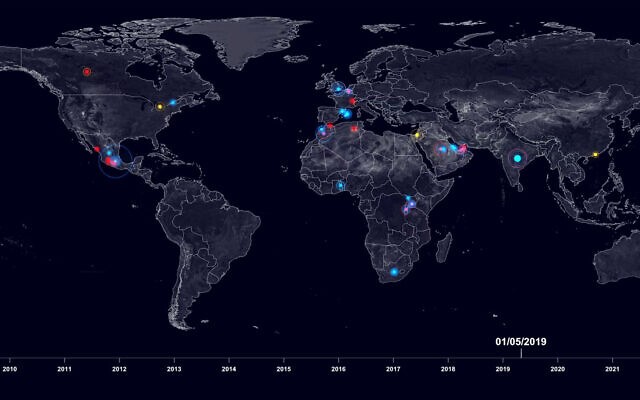
An interactive online platform created by research agency Forensic Architecture, and supported by Amnesty International and the internet watchdog group Citizen Lab, has mapped the global spread of the spyware Pegasus, made by Israeli cybersecurity firm NSO Group.
Enitled Digital Violence: How the NSO Group Enables State Terror, the website shows, for what is said to be the first time, geographic areas in which Pegasus spyware has been deployed worldwide, and interviews lawyers, activists and other civil society figures about their experiences.
“The company’s Pegasus spyware has been used in some of the most insidious digital attacks on human rights defenders,” Amnesty International has said on its website. “When Pegasus is surreptitiously installed on a person’s phone, an attacker has complete access to a phone’s messages, emails, media, microphone, camera, calls and contacts.” On July 13, 2020, the Tel Aviv District Court ruled in favor of Israel’s Ministry of Defense (MOD) and the spyware company NSO Group in a lawsuit submitted by Amnesty International which demanded that the MOD revoke the export license of the cyber security company.
“The investigation reveals the extent to which the digital domain we inhabit has become the new frontier of human rights violations, a site of state surveillance and intimidation that enables physical violations in real space,” said Forensic Architecture researcher Shourideh Molavi in the Amnesty statement.
Amnesty said that the online platform is “one of the most comprehensive databases on NSO-related activities,” including information about export licenses, alleged purchases, digital infections, and the physical targeting of activists after they were targeted with spyware, including intimidation, harassment, and detention.
The platform also sheds light on the complex corporate structure of NSO Group, based on new research by Amnesty International and partners. The research details changes to the NSO Group over the years, from its incorporation in Israel in 2010 to the purchase of a majority stake in the company by US private equity firm Francisco Partners in 2014 and the management buyout backed by UK private equity firm Novalpina Capital in 2019. The research flags the jurisdictions in which NSO group, and its operating entities are located, including Israel, the Virgin Islands, the Cayman Islands, Cyprus, the US and the UK, and the public funds that have invested in the company.
“For years, NSO Group has shrouded its operations in secrecy and profited from working in the shadows. This platform brings to light the important connections between the use of its spyware and the devastating human rights abuses inflicted upon activists and civil society,” said Danna Ingleton, deputy director of Amnesty Tech.
“Amnesty International’s Security Lab and Citizen Lab have repeatedly exposed the use of NSO Group’s Pegasus spyware to target hundreds of human rights defenders across the globe,” Amnesty said on its website. The organization called on the NSO Group “to urgently take steps to ensure that it does not cause or contribute to human rights abuses, and to respond when they do occur. The cyber-surveillance must carry out adequate human rights due diligence and take steps to ensure that human rights defenders and journalists do not continue to become targets of unlawful surveillance.”
In October 2019, Amnesty International said that Moroccan academic and activist Maati Monjib’s phone had been infected with Pegasus spyware. “He continues to face harassment by the Moroccan authorities for his human rights work,” Amnesty said. In December 2020, Monjib was arbitrarily detained before being released on parole on March 23, 2021, Amnesty added. Monjib was released from the Al Arjat 2 prison near Rabat. On March 4, 2021, Monjib started a hunger strike in protest of the one-year prison sentence he received on January 27. With a heart condition and diabetes, there was little doubt that his life was endangered.
Related: Full online report Digital Violence: How the NSO Group Enables State Terror
CPI Posts: